About Apple security updates
Find 2,2 dimeth and related products for scientific research at MilliporeSigma.
For our customers' protection, Apple doesn't disclose, discuss, or confirm security issues until an investigation has occurred and patches or releases are available. Recent releases are listed on the Apple security updates page.
For more information about security, see the Apple Product Security page. You can encrypt communications with Apple using the Apple Product Security PGP Key.
Apple security documents reference vulnerabilities by CVE-ID when possible.
watchOS 3.2.2
- Jun 05, 2018 As described in B4-2.2-06, Project Eligibility Review Service (PERS), certain manufactured home projects must be submitted to PERS. Lenders must perform a pre-PERS submission review to confirm the project meets the Full Review and other requirements. The condo project must meet all Full Review requirements, as applicable.
- Gt 2 (2) or g = 2 2 t. If the initial velocity u = 0 (3) where t and s = time taken to hit the ground and height of fall respectively, and g = gravitational acceleration. Thus for a mass (m) of 400g to take the time t = 0.8 seconds to fall freely from a height s = 0.75metres to hit the nut, the.
- As described in B4-2.2-06, Project Eligibility Review Service (PERS), certain manufactured home projects must be submitted to PERS. Lenders must perform a pre-PERS submission review to confirm the project meets the Full Review and other requirements. The condo project must meet all Full Review requirements, as applicable.
Released May 15, 2017
AVEVideoEncoder
Available for: All Apple Watch models
Impact: An application may be able to gain kernel privileges
Description: Multiple memory corruption issues were addressed with improved memory handling.
CVE-2017-6989: Adam Donenfeld (@doadam) of the Zimperium zLabs Team
CVE-2017-6994: Adam Donenfeld (@doadam) of the Zimperium zLabs Team
CVE-2017-6995: Adam Donenfeld (@doadam) of the Zimperium zLabs Team
CVE-2017-6996: Adam Donenfeld (@doadam) of the Zimperium zLabs Team
CVE-2017-6997: Adam Donenfeld (@doadam) of the Zimperium zLabs Team
CVE-2017-6998: Adam Donenfeld (@doadam) of the Zimperium zLabs Team
CVE-2017-6999: Adam Donenfeld (@doadam) of the Zimperium zLabs Team
Entry updated May 17, 2017
CoreAudio
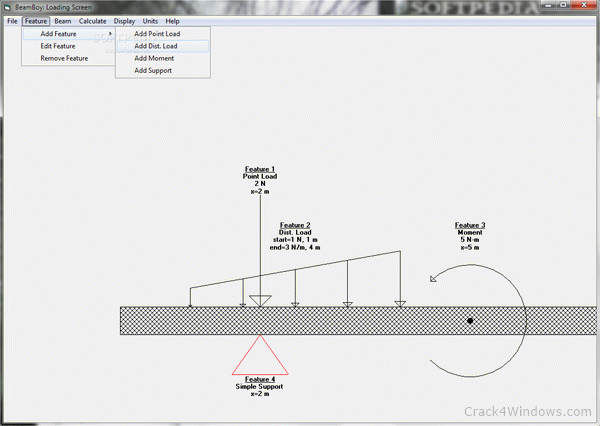
Beamboy 2.2 Full Hd
Available for: All Apple Watch models
Impact: An application may be able to read restricted memory
Description: A validation issue was addressed with improved input sanitization.
CVE-2017-2502: Yangkang (@dnpushme) of Qihoo360 Qex Team
CoreFoundation
Available for: All Apple Watch models
Impact: Parsing maliciously crafted data may lead to arbitrary code execution
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2017-2522: Ian Beer of Google Project Zero
Entry added May 19, 2017
CoreText
Available for: All Apple Watch models
Impact: Processing a maliciously crafted file may lead to application termination
Description: A denial of service issue was addressed through improved validation.
CVE-2017-7003: Jake Davis of SPYSCAPE (@DoubleJake), João Henrique Neves and Stephen Goldberg of Salesforce
Entry updated June 7, 2017
Foundation
Available for: All Apple Watch models
Impact: Parsing maliciously crafted data may lead to arbitrary code execution
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2017-2523: Ian Beer of Google Project Zero
Entry added May 19, 2017
IOSurface
Available for: All Apple Watch models
Impact: An application may be able to gain kernel privileges
Description: A race condition was addressed through improved locking.
CVE-2017-6979: Adam Donenfeld (@doadam) of the Zimperium zLabs Team
Entry updated May 17, 2017
Kernel
Available for: All Apple Watch models
Impact: An application may be able to execute arbitrary code with kernel privileges
Description: A race condition was addressed through improved locking.
CVE-2017-2501: Ian Beer of Google Project Zero
Kernel
Available for: All Apple Watch models
Impact: An application may be able to read restricted memory
Description: A validation issue was addressed with improved input sanitization.

CVE-2017-2507: Ian Beer of Google Project Zero
CVE-2017-6987: Patrick Wardle of Synack
SQLite
Available for: All Apple Watch models
Impact: A maliciously crafted SQL query may lead to arbitrary code execution
Description: A use after free issue was addressed through improved memory management.
CVE-2017-2513: found by OSS-Fuzz
SQLite
Available for: All Apple Watch models
Impact: A maliciously crafted SQL query may lead to arbitrary code execution
Description: A buffer overflow issue was addressed through improved memory handling.
Beamboy 2.2 Full Movie
CVE-2017-2518: found by OSS-Fuzz
CVE-2017-2520: found by OSS-Fuzz
SQLite
Available for: All Apple Watch models
Impact: A maliciously crafted SQL query may lead to arbitrary code execution

Description: A memory corruption issue was addressed with improved memory handling.
CVE-2017-2519: found by OSS-Fuzz
TextInput
Available for: All Apple Watch models
Impact: Parsing maliciously crafted data may lead to arbitrary code execution
Beamboy 2.2 Full Version
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2017-2524: Ian Beer of Google Project Zero
WebKit
Available for: All Apple Watch models
Impact: Processing maliciously crafted web content may lead to arbitrary code execution
Description: Multiple memory corruption issues were addressed with improved memory handling.
Beamboy 2.2 Full Movie
CVE-2017-2521: lokihardt of Google Project Zero
Additional recognition
Beamboy 2.2
Kernel
We would like to acknowledge Orr A. of Aleph Research, HCL Technologies for their assistance.